TNS (Transparent Network Substrate) is the propritary protocol used by Oracle between their client applications and their database servers.
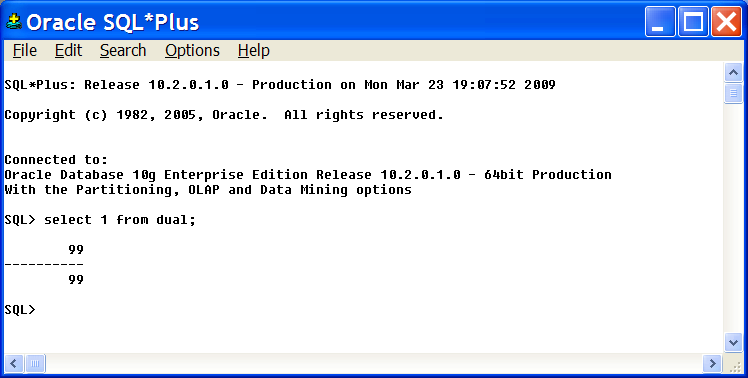
In this workshop, we are going to demonstrate how to use TcpCatcher as a 'TCP proxy' in order to interfere in a TNS communication between an SQLPlus client and an Oracle database server. For demonstration purpose, we are going to modify a simple SQL request on the fly, replacing "select 1 from dual" with "select 99 from dual".
This workshop was realised with an old version of TcpCatcher but will be doable in the very same way with the last version.
- Suppose we have an Oracle server database running on host ORACLEHOST, listening on port 1521, and our SQLPLus client is running on our local host.
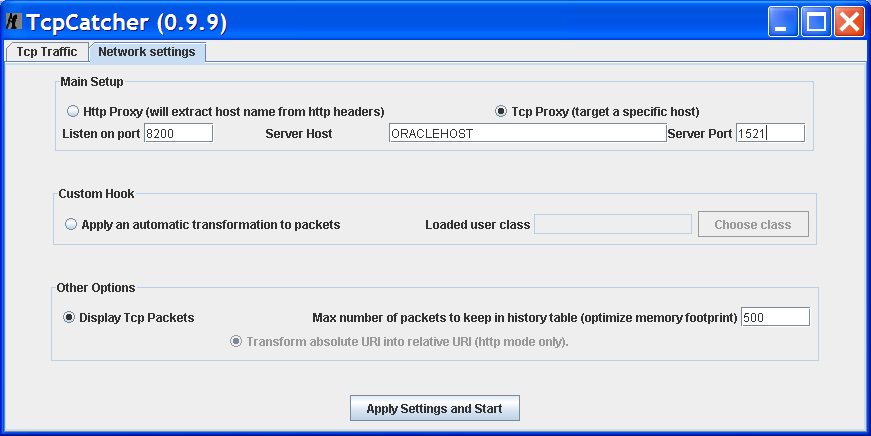
- Start TcpCatcher, in the Settings panel choose the Tcp Proxy mode, and set Server Host to ORACLEHOST, Server port to 1521.
Click on "Apply Settings and Start".
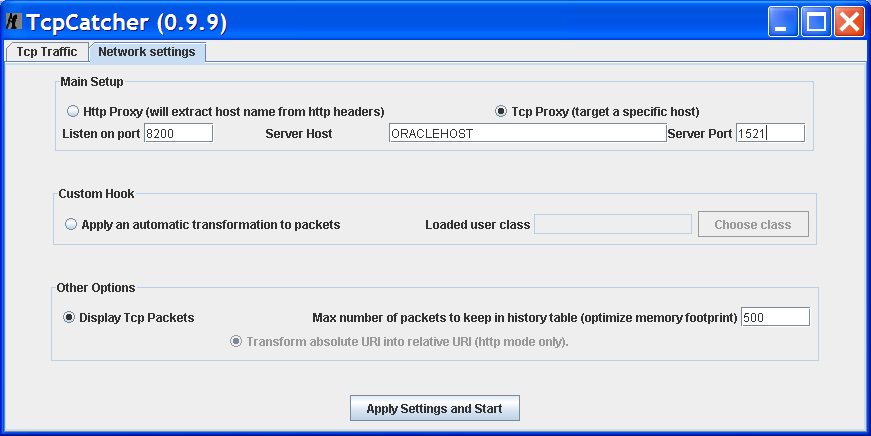
- Now, we need to set up SQLplus client to connect to our local TcpCatcher proxy instead of ORACLEHOST.
In order to achieve this, let's add a TCPCATCHER entry in our tnsnames.ora file :
-
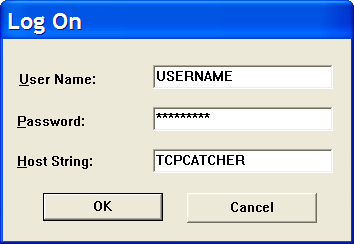
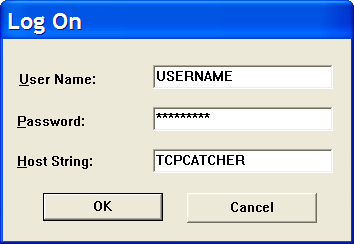
Start SQLPlus, entering usual USER / PASSWORD but TCPCATCHER as the connection alias.
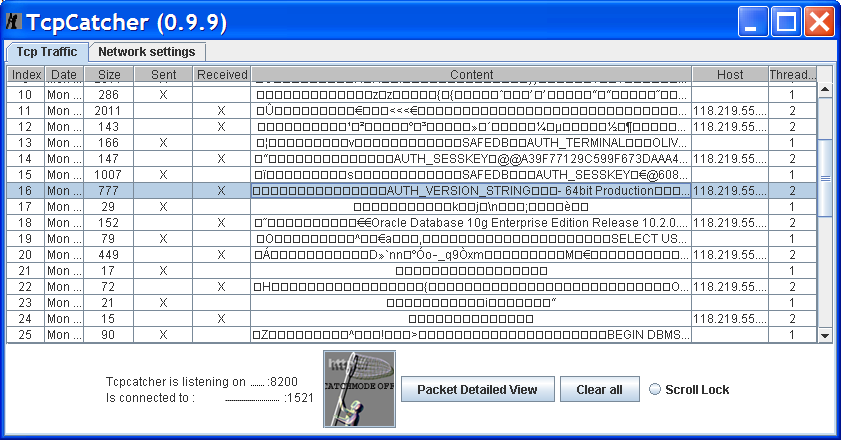
- You should now see the TNS handshake communication going through TcpCatcher.
Check also that you can send SQL requests normally from SQLPlus.
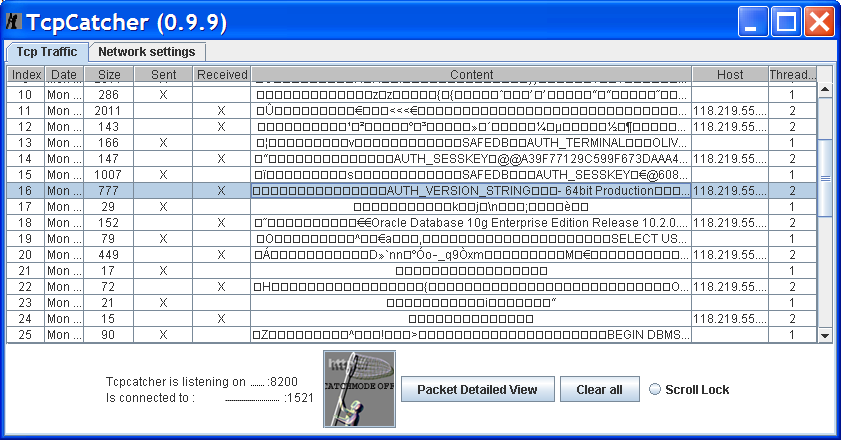
- Now, turn on CatchMode in TcpCatcher and send "select 1 from dual;" from SQLPlus.
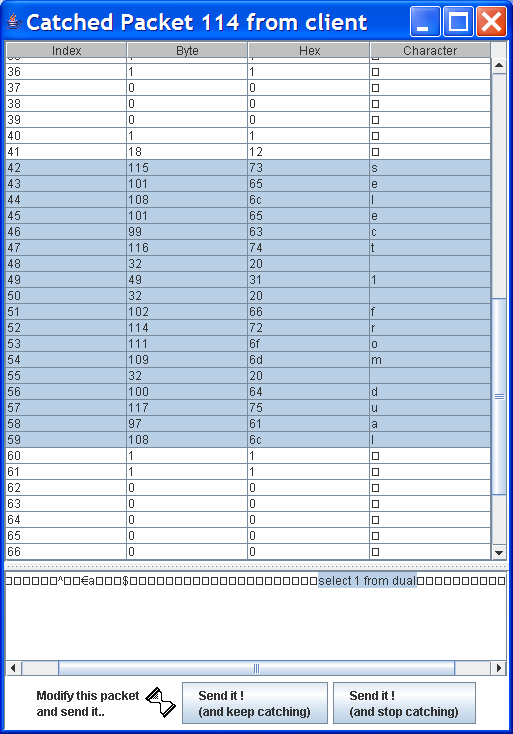
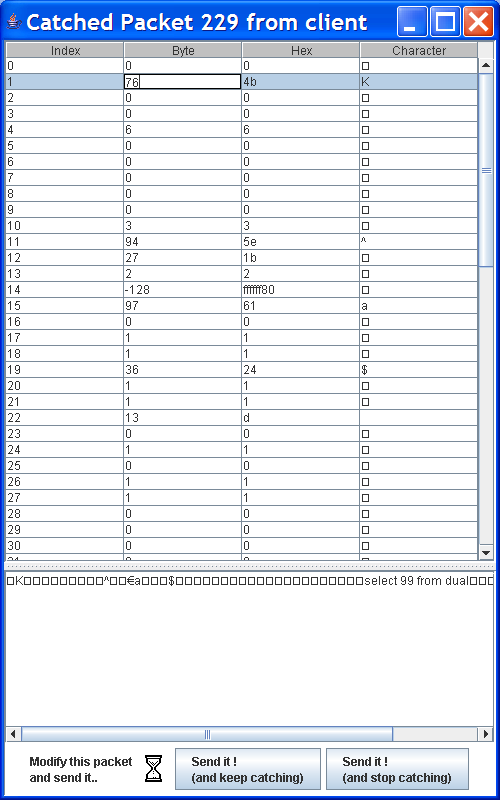
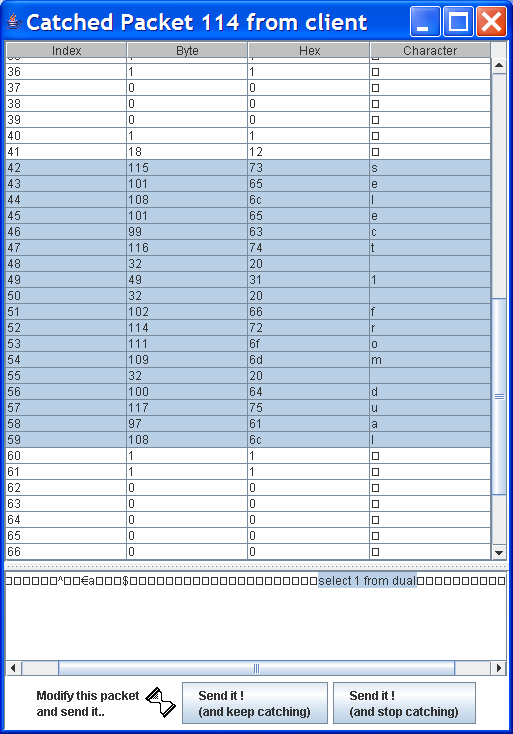
Packet is intercepted, try to just replace "select 1" with "select 99" and click "Sent it (and stop Catching)".
-
Well, this provokes an unexpected shutdown of SQLPLus. Is Oracle handling exceptions...?
-
Actually, it not that simple, notice that just before "select 1 from dual" there is
an octet which value is 12.
That octet is carrying the length of the request, we need to change that octet too
since we are changing the length of the request. We are going to replace it with value 13.
May be, looking a little at the tns packets you have also noticed that the first two octets are carrying the length of the packet. We need to change them too.
In our case, first octet is 0, second is 75. We just need to replace the second 75 with 76.
Let's try again.
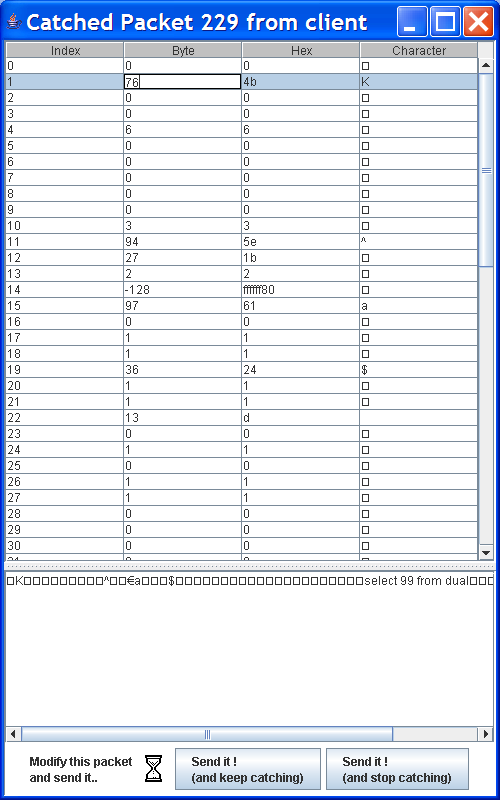
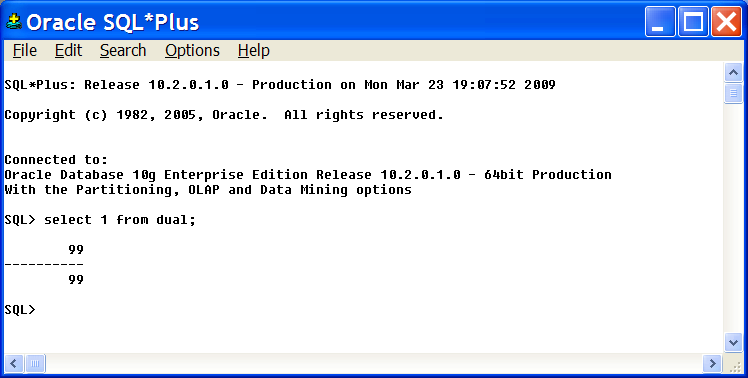
- That time it worked :